Mindset
Having the right mindset is crucial for success. This entails being adaptable, open to learning, and resilient in the face of challenges. A growth mindset encourages business leaders to embrace obstacles as opportunities for development and innovation.
Model
This refers to the business model, which outlines how a company creates, delivers, and captures value. A well-defined business model includes understanding the target market, revenue streams, and competition. It serves as the framework for generating profit and sustainability.
Method
Methods encompass the strategies, processes, and practices a business employs to execute its model effectively. This can involve operational procedures, marketing strategies, and customer engagement practices. The right methods help streamline operations and enhance productivity.
Back Story from Abi BC
I had a rough time getting through grade school (up to grade 6). That next summer, a light bulb was developing over my head and was fully formed by Grade 9. I was helping my grade 7 math teacher, teach my class mates Algebra. By the time I got to grade 9, I had taught myself up to grade 11 drafting. As time went on, I began to realize that the following text of this page was a great way to describe what happened to me.
During these early years of my life, I also gained the wisdom of 2 main points. One, that it is human that we learn with repeating something that is new to us. And second that being human, we are not perfect and that we can not create something that is perfect. To be human is to error!
Step 1
It is simple as ABC123!
Think of it as being simple and it will be simple!
Step 2
Analogy 1
All cars are the same to use:
This is the most important analogy!
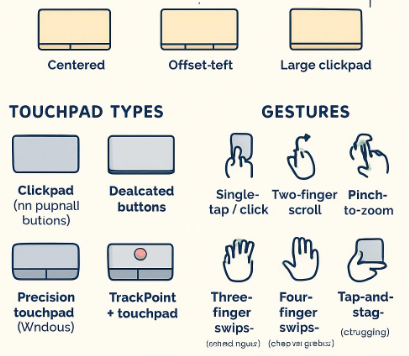
All cars have a steering wheel, accelerator, brake pedal, speedometer and everything else is somewhere in the car. That is the same with all computers and all software. They all have a keyboard, screen, software and everything else is in the hard drive.
This relates to the fact that all computers are the same! Just subtle differences inside and out. Just like car and pickups.
Analogy 2
Computer Compared to a Car
A computer is like a car in several ways:
Engine vs. Processor: The car's engine powers the vehicle, just as the computer’s processor (CPU) executes commands and processes data. Both are essential for performance; without a strong engine or a processor!
Operating System vs. Dashboard: The computer’s operating system (OS) acts like a car’s dashboard. The dashboard displays critical information (speed, fuel level) and allows the driver to interact with the vehicle’s functions (radio, navigation). The OS manages software and hardware resources, making the user experience smooth and intuitive.
Memory vs. Fuel Tank: The memory (RAM) in a computer is similar to the fuel tank in a car. Just as a full fuel tank provides the energy needed for the car to run, sufficient RAM enables the computer to operate multiple applications simultaneously without slowing down.
Storage vs. Trunk: A car’s trunk provides storage space for items, while a computer's hard drive (or SSD) stores data and files. Both are necessary for keeping essential items and information available for use when needed.
Analogy 3
Computer Compared to the Human Body
Computers can also be compared to the human body in interesting ways:
Processor vs. Brain: The computer’s processor functions like the human brain, processing information, making decisions, and controlling actions. Just as the brain interprets signals from the body and coordinates responses, the processor interprets inputs and executes tasks.
Memory vs. Nervous System: The computer's memory (RAM) is akin to the human nervous system, which facilitates communication between different body parts. RAM allows for quick access to information needed for immediate tasks, much like the nervous system relays signals rapidly for reflexes and actions.
Operating System vs. Consciousness: The OS of a computer is comparable to human consciousness. It governs interactions, manages resources, and maintains the operation of various software applications, similar to how consciousness directs thoughts, feelings, and actions.
Data Storage vs. Long-term Memory: The data storage in a computer (hard drives) resembles human long-term memory, where information is kept for future reference. Just as people retrieve memories when needed, computers access stored data to perform functions.
Step 3
Spend a little bit of time each day, that works for you to sit down and close your eyes and think about the simplicity of these ideas above. Within no time, you will realize you can absorb the info on this website page and now you will enjoy using your computer even more.
Conclusion
These analogies highlight the functionalities and relational structures between computers, cars, and the human body, illustrating complex systems through more familiar concepts. To help you realize that it is ALL as simple as ABC123! Funny note: ABC is the initials of my name. That is why the business name is ABC Enterprise.